Cybersecurity and Your Material Handling System: What You Need to Know in the IoT Era

According to recent findings from Research and Markets, the global material handling equipment market is projected to reach $156 billion by 2026, a compound annual growth rate (CAGR) of 4.7%. That uptick in investment has been driven by operations replacing outdated material handling equipment, software, and processes as they embark on a digital transformation intended to help them be more responsive and efficient in meeting customer demands.
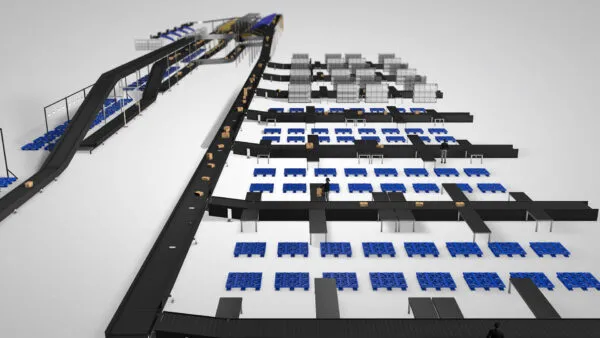
Enabling that digital transformation are innovations such as the Internet of Things (IoT), which connects devices — including industrial controls, sensors, conveyors, sorters, automated storage and retrieval systems (AS/RS), robotics, and a multitude of other automated and semi-automated material handling systems — and allows them to share data over the Internet and other communication networks, such as cloud-based services. The increased connectivity enables an operation to collect and analyze information about equipment function and product movement through a facility. This, in turn, increases visibility to enable managers to quickly adapt to changing conditions and maintain productivity.
With anticipated automation investment as high as it is, chances are your organization is among those considering investing in a greenfield facility with a brand-new automated material handling, distribution, or parcel handling system. Or, it might be planning a brownfield expansion, upgrade, or retrofit of an existing operation. Either way, part of the benefit you’re likely expecting to receive is increased connectivity and operational visibility from IoT-enabled technologies.
However, with that connectivity also comes a greater risk for a cybersecurity incident, such as a virus, malware, or ransomware attack. In the United States, ransomware targeted 14 out of 16 critical infrastructure sectors last year, according to a report from the Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), and the National Security Agency (NSA). Further, the agencies note that while organizations of all sizes were targeted, ransomware operators were increasingly moving away from large, high-profile companies. Instead, they’ve shifted focus to mid- and smaller-sized operations that tend to have fewer resources to protect against and mitigate cyberattacks.
For all these reasons, it’s therefore become that much more important to formulate your material handling systems cybersecurity practices sooner than later, regardless of your organization’s size or the scope of your operational investment.
Several best practices in cybersecurity for automated material handling, distribution, or parcel handling systems exist. They include:
- Keep up with updates. Whether you’re upgrading or expanding an existing system or implementing an entirely new one, routinely checking for and applying patches and updates as they are released — for all of your software and firmware systems — should be an integral part of your ongoing preventive maintenance program. Don’t be the operation that falls into the “set it and forget it” trap. The vendors and suppliers of your material handling and automation systems are continuously updating their software to defend against the latest security breaches and close previously undetected points of unauthorized access.
Some operations avoid updates out of fear that they might disrupt current operations. While it is true that does happen on occasion, if you are continuously backing up your data (encrypted and stored offsite in the Cloud), recovery is assured with minimal downtime. In contrast, the prolonged downtime associated with a cybersecurity breach that renders your operation completely incapacitated is exponentially harmful to the bottom line.
- Involve the Information Technology (IT) department. Every system design concept today — whether greenfield or retrofit — should be vetted by the IT department prior to signing off on the project. IT can help operations find the optimal balance between security and usability, often assigning specific IP addresses for different devices and helping to define the appropriate segregation points between equipment within a network.
For example, there’s no need for the controls of a transport conveyor to be connected to order or customer data stored in a database accessible via your warehouse management system (WMS). Correctly applying network segregation and monitoring all points of information ingress and egress typically falls into the realm of IT; leverage their expertise to ensure the data flow is appropriate and adequately secure.
- Routinely assess the age of your systems and devices. Not only does this include the large pieces of automated equipment, but also — and often more importantly — the small devices that are integrated into your system. These include Automatic Identification and Data Capture (AIDC) technologies, such as sensors, bar code readers, photo eyes, and laser scanners, as well as controls like programmable logic controllers (PLCs), drives, and more. All of these transmit real-time data for IoT monitoring and communications. They may or may not be running embedded firmware that also requires updates. Or they may be so old they are no longer supported by their original equipment manufacturer (OEM). Either scenario can increase an operation’s vulnerability to a cyberattack.
- Vet your software provider’s security protocols. Any software provided with the new or updated system — such as Warehouse Control Systems (WCS) or Warehouse Execution Systems (WES) — should be assessed for its security capabilities. Ask the supplier about security testing, penetration testing, and security protocols that verify the software’s hardening. Also inquire about patch analysis and distribution cycle frequency, how the software will be securely integrated with any existing operational software already in place, and what degree of support will be provided both during the installation and post-commissioning. Some software providers also offer ongoing maintenance and support contracts with different pricing models (annual fee versus pay-per-incident). All of these factors should be considered through a cybersecurity lens prior to signing any contracts.
- Train your personnel to be cognizant of threats. As phishing schemes continue to become more sophisticated and personalized, anyone with an email address in your operation can fall victim to inadvertently downloading or opening a file with malicious content. Alternately, in some instances hackers have gained control of a network by planting an unmarked thumb drive on the ground or floor of an office. An unsuspecting employee who assumes it was dropped by a colleague will likely plug it into the nearest computer to see if they can determine who it belongs to — unleashing a virus, malware, or ransomware into the network. In addition to firewalls and spam filters, regularly training your personnel to be aware of potential threats to network security such as these will help reduce the risk of a compromising incident.
Looking for more insight into cybersecurity for your new or upgraded material handling system? Connect with us; we’re happy to offer more personalized guidance specific to your operation.
Author
Eric Kershner, Systems Consultant, eric@designedconveyor.com